As the world is moving towards adopting cloud services, AWS (Amazon Web Services) has been the top selection for most. Amazon Web Services has actually been around since 2006 however users are still wondering about the best practices and associated AWS security risks. Constructing a robust cloud infrastructure that includes comprehensive cloud security architecture with an understanding of all its blind and user models is key to having a secure cloud.
8 Major AWS Security Risks
1. Unrestricted and long-lived access to S3 buckets
S3 (Simple Storage Service) lets users keep data that can be easily and securely retrieved. In this, users select a region and create a bucket to upload data. The S3 system uploads and stores data on multiple data centers in that region and also fixings all found lost redundancy.
S3 buckets are susceptible to ransomware attacks if they permit unfiltered access to all users. Attackers can use an account that has read/write permission and use it to encrypt admin and also core documents and folders. Aside from this, attackers can also rewrite settings or set up malware within the application using such privileges.
Therefore, AWS users must approve and manage permissions for those who have access to these buckets. Permissions can be of the list following kinds: edit permission, view permission, upload/delete, and list. Reviewing permission for all these buckets is an essential action to mitigate AWS security risks.
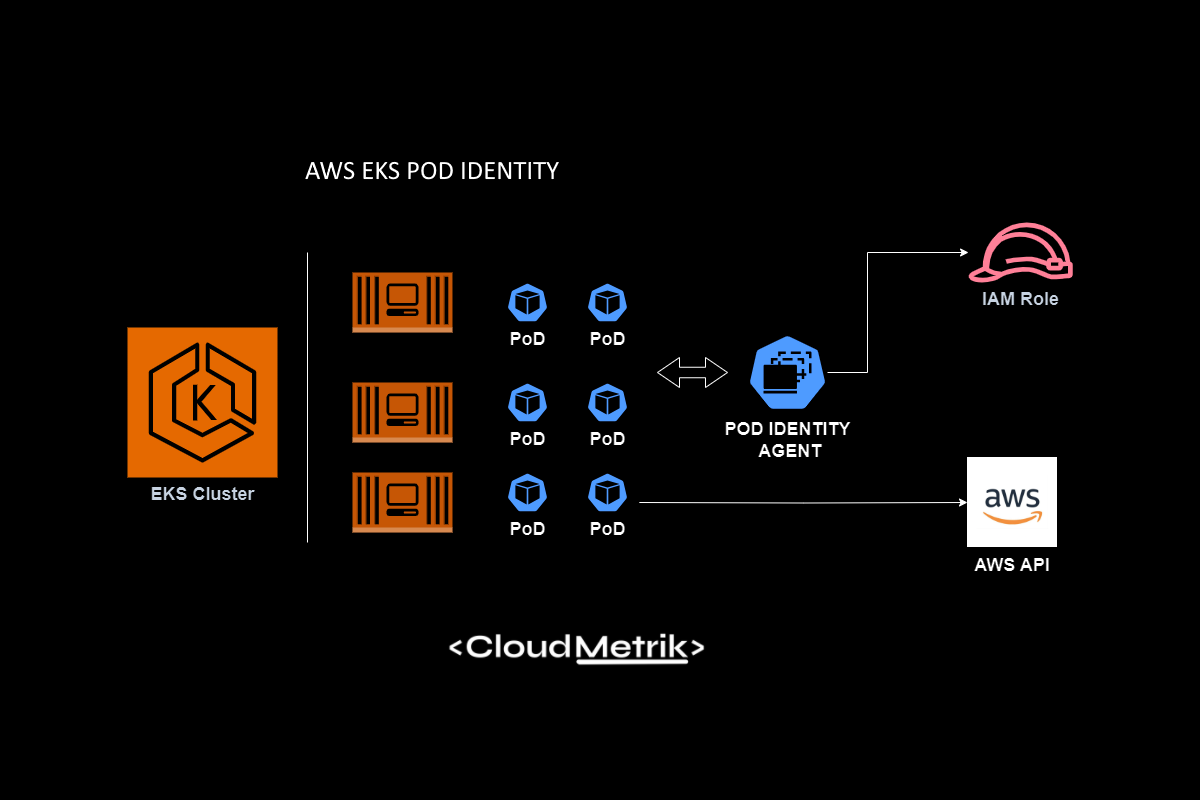
You will need to implement temporary access with the IAM Roles strategy when accessing your data. You can create custom policies with some conditions like IP address for your IAM roles. So, you can define a secure process between your application and S3 Buckets.
2. Undetected request events to your S3 Buckets
S3 Buckets can become targets for information theft because they handle objects and store application files. Cyber-attacks leading to data leaks consist of countless requests for accessing data in these buckets. And in the absence of bucket logs, these requests go undetected until it is too late.
S3 Buckets do not generate logs by default given that it needs to be turned on manually. Once enabled, S3 buckets will create access logs for any type of request made to the buckets with details such as the type of request, the resource used for the request, and date-time stamps. Having gain access logs helps in assessing AWS security risks by keeping an eye on requests and also recognizing the type of requests made. Having access logs helps in assessing AWS security risks by monitoring requests and identifying the type of requests made.
🔐An AWS Security Audit would be a great approach to identify such misconfiguration.
3. Malevolent AWS API requests
There are multiple AWS APIs available in public and the attackers could use these endpoints to explode some of your architecture details. They can try to sniff access details from your application’s communication with AWS services like DynamoDB, SQS, SNS, API Gateway,…
Then the attackers can use this information to inject malicious codes right into API to launch DDoS attacks or use these infected APIs for SQL Injection for an extensive cyberattack.
You need to always use proper encryption options with these AWS services at this point. Also, it is recommended that you should use AWS SDK when developing AWS-integrated applications. Because AWS SDK signs your requests by default.
For monitoring, Amazon CloudTrail allows users to access the complete history of all API calls made to the account. These logs include Request, Response, IP address as well as date-time stamps. Once these logs are created, they are stored in a pre-designated S3 bucket. Having CloudTrail enabled will certainly help you detect any kind of AWS security risks by monitoring all API calls. Also, you can get notified with CloudTrail Event with some specific security issues like root user login.
4. Unfiltered traffic from untrusted sources
When traffic has unrestricted access to your deployed AWS instances or load balancers, there is a possibility that attackers can gather information about the application to launch an attack. By limiting particular traffic to specific instances, you will stop attackers from gaining insight into the application.
Without an effectively configured network, attacks such as DDoS can be launched from a group of IPs and also can rapidly overwhelm a system. To prevent such attacks you require to configure the network to deny traffic from suspicious sources. This also aids in reducing the attack area of an application by limiting traffic as well as controlling access.
Security Groups act like a firewall by allowing just specific traffic to any instance. As an example, the EC2 instance may have multiple Security Groups assigned to it, for which the rules can be updated at any time. As well as only the allowed traffic can access the instance. These rules define specific sources for accessing the instance by using protocols such as ICMP or TCP along with destination ports. To stay clear of any AWS security risks only specific IP addresses or ranges ought to be allowed access.
NACL is an additional layer of security that manages the traffic to and also from a subnet. Similar to other security groups you can set up NACL with security rules. In NACL, rules are evaluated based on the rule number. The first rule that matches a request is offered priority and implemented. To avoid any type of AWS security risks, check to see if an NACL rule allows all ports or IP addresses. This will certainly make the system vulnerable, so remove the rule as well as create new restrictive rules for appropriate ports or IP.
5. Incorrect permission and privileges
Not all users need access to all folders and divisions of the application. For instance, non-admin users would not require access to the control panel or admin files. Identity and Access Management allows users to manage account access by setting up user accounts and also permissions. IAM also allows for the creation of user groups which assists in assigning permissions collectively to users who belong to a specific group.
Identity and Access Management enables users to manage account access by setting up user accounts and permissions. IAM also enables the creation of user groups which helps in assigning permissions collectively to users that belong to a specific group. While assigning permissions, you need to understand the demands and requirements of the set of permissions. Review all users who have higher access privileges and regularly update users based on their functions. Also, you need to prevent using AWS Managed Policies. You can create custom policies based on the application stage and user role.
6. Login and credential theft
Plenty of cyber-attacks on cloud services are based on credential theft. Credentials are the gold mines for hackers, allowing them to totally take over an account. Cyberattacks faced by establishments such as CodeSpaces and Timehop are an example of exactly how extensive damage can be done by credential theft. There are some ways to secure your account and sign-in information:
- 2 Factor Authentication or Multi-Factor Authentication can protect accounts in case credentials are stolen
- Continuous monitoring for failed or anonymous logins
- Store your application and system logs with strict rights
- Do not push your credentials git repositories and logs
- You can make use of services such as AWS Secrets Manager to rotate login credentials
7. Vulnerable multi-tenant cloud infrastructure
The notion that multi-tenant systems have more security risks is not correct. Rather the security of your system and also infrastructure figures out the level of security. AWS has adopted numerous measures to ensure the proper partition of data between users as well as to ensure that there are no data leaks in the case of multi-tenant systems. Still, users can take extra precautions in areas as pointed out listed below:
- Secure access for end users — like Oauth2
- Central control panel and infrastructure
- Monitoring the runtime and services actively
- Vulnerability and also automated patching management
- Invest in Private Networking like DirectConnect
8. Protect your public endpoints with WAF
If you need to serve API endpoints or web applications in public, you need to monitor and take action against popular attack types like DDoS, ReDoS, XSS, … in real-time.
You can easily create a powerful layer-7 firewall with AWS WAF service against OWASP Top 10 rules. AWS WAF is a web application firewall that lets you monitor the HTTP and HTTPS requests that are forwarded to your protected web application resources. You can protect the following resource types:
- Amazon CloudFront distribution
- Amazon API Gateway REST API
- Application Load Balancer
- AWS AppSync GraphQL API
- Amazon Cognito user pool
You can get benefit from managed rules to mitigate attacks with minimum effort. Also, if you want to create a more resilient application, you can create your own rule sets. You can evaluate the incoming requests in real-time and accept or deny them with such information as IP address, HTTP header, originated country, and the presence of SQL/XSS code that is likely to be malicious. For instance, if you do not serve in a specific country, you can block all requests coming from this country.
Conclusion
As more and more companies are moving toward cloud-based systems, AWS security risks continue to increase. Security breaches and cyberattacks can trigger a tremendous influence on financial and brand value. To ensure that your cloud services are completely secure, you will certainly require an extensive AWS security audit which can detect security gaps as well as offer a comprehensive fixing plan and guidance. We at CloudMetrik have a vulnerability scanner and audit system with more than 300 tests, developed by a team of security experts with comprehensive experience. From network systems to business logic, CloudMetrik’s tool checks all avenues of your system and also provides a comprehensive report for an in-depth understanding of your security standards.