Since 2020, AWS held 76% of enterprise cloud adoption, a fact measuring the power and value AWS holds. Nevertheless, with great power also comes a greater probability of risk, as well as customers using AWS, have found themselves the targets of many data breaches over the past year. AWS enables enterprises to upload and distribute data with unique effectiveness, but it comes with a unique set of vulnerabilities easily overlooked by users. This danger is precisely why AWS is working hard to protect their infrastructure and secure their platform to protect things like customer information. Nevertheless, AWS operates under the Shared Responsibility Model; this means that the customer is responsible for keeping everything secure in their cloud. This includes services and customizable configurations for smart use of your cloud. AWS provides a range of security tools and services to help make your life easier when it comes to securing your cloud. This article will introduce some of the AWS security services, tools, and solutions that you can use as a customer.
What are AWS Security Tools and Services?
AWS Security Tools and Services are a variety of services provided by AWS that spread several areas of security, including data protection, identity and access management, infrastructure security, threat detection and continuous monitoring.
Data protection: AWS is aware of the importance of securing data and ensuring that it is not lost in the transfer. Their services help you meet basic security, privacy, and compliance needs. Features contain encryption, data replication, and data monitoring. An example of a data protection service from AWS is Amazon Macie.
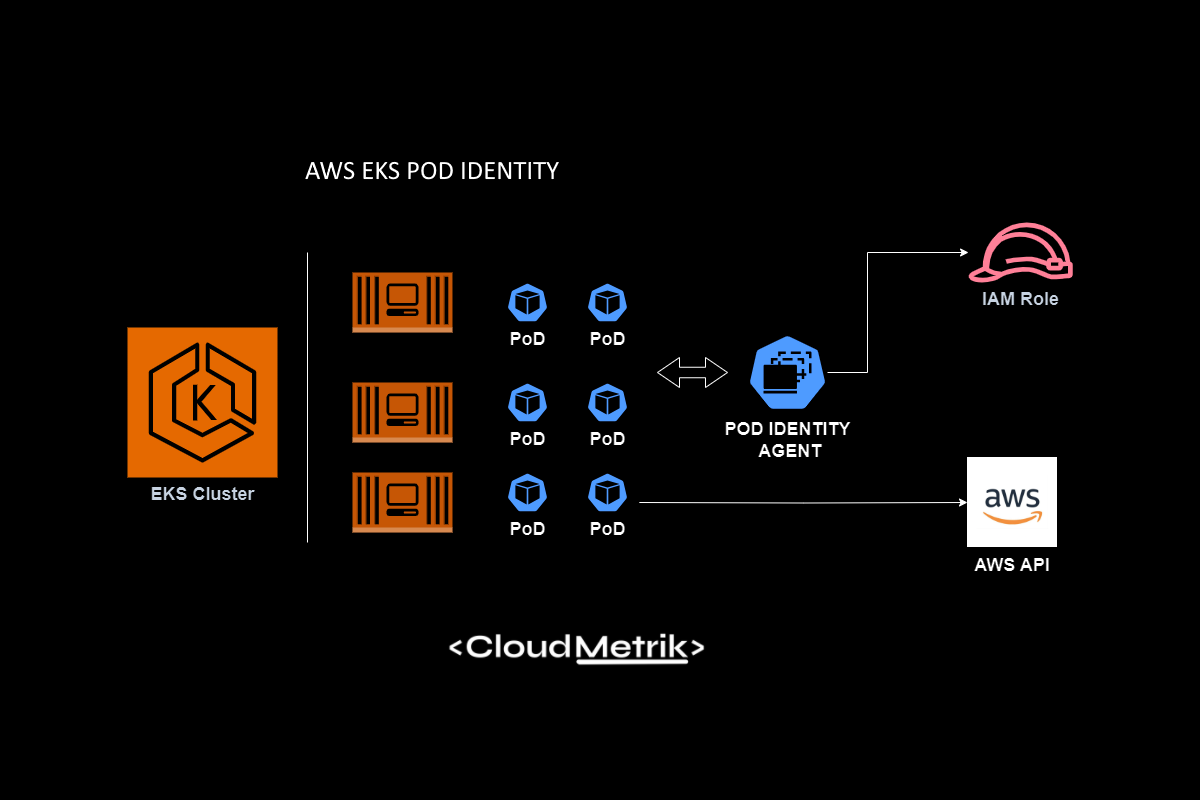
Identity & Accessibility Administration: AWS is aware of the need to manage identities, so they provide a comprehensive list of tools and services to help you manage your identity in the cloud. The goal is to control the resources and actions that identities can use and manipulate.
Infrastructure Security: Infrastructure protection is a critical component of information security, helping to ensure that everything in your workload is safe from vulnerability, exploitation, or unwanted access. Although the infrastructure is largely managed by AWS, they also provide some additional resources, such as AWS WAF, to manage the security of the configurable infrastructure.
Threat Detection: When in the cloud, you need constant assurance that your security posture is strong and that you have the right configurations to optimize security. AWS provides services such as Amazon GuardDuty that increase visibility into your deployment and operations, as well as monitor identity behavior to help detect threats.
Account vs. Application vs. Service Security on AWS, one thing to note about AWS services and tools is that there are distinctions in what these sources are helping to secure. AWS differentiates between account security and application and service security.
Account: Securing an identity, whether personal or non-personal, requires a different approach to security. This is where IAM practices stand out, as AWS encourages control identities’ ability to access sensitive data or manipulate privileges. This can help avoid concerns like privilege escalation if someone’s credentials are compromised. An example is AWS IAM, a service that provides security practices such as SSO or MFA and that determines and manages the permissions of identities in your cloud.
Application & Service: Applications and services within AWS are vulnerable to threats such as external attacks from malicious people or even vulnerabilities existing from the development process, so they need their own security resources. An example would be Amazon Inspector, a service for vulnerability management of applications deployed on EC2. Now that we’ve explored the different purposes and types of AWS security tools, let’s apply this information and explore the best services and features customers can use today.
Top 11 AWS Security Tools.
AWS Security Hub
Collection and Identification, AWS Security Hub is a cloud security posture management service that collects and identifies security data from across AWS accounts, services, and supported third-party partner products. It collects your security alerts (findings) in a standardized format so you can take action easily. Security Hub makes it easy to understand and improve your security posture through automated integrations with other AWS services like AWS Systems Manager or AWS partner products. It can also detect the severity of the finding. Many roles may find themselves tasked with managing the secure use of the cloud, but in particular, this may be used by Cloud Security Analysts.
AWS Shield
Infrastructure Protection, AWS Shield protects all your applications running on AWS from DDoS attacks, or Denial-of-Service attacks. These guidelines protect the environment of your application. The good thing is that Shield is integrated by default with services like ALB, API Gateway, and CloudFront. You can also choose the Advanced version if you want more transparency regarding DDoS attacks to AWS. The target audience for this service is DevSecOps and cloud administrators.
AWS Identity Access Management (IAM)
Identity & Access Management, AWS IAM provides identity and access controls in the environment. Specifically, it offers granular control over which identities (person and nonperson) can access and perform. You can create your roles and custom policies securely using strict conditions. Typical users of this are IT Managers or Cloud Admins.
AWS IAM Analyzer
Identity & Access Management Usage Reporting, Building from the insights and controls AWS IAM provides, the complexities of managing the permissions of identities can get unruly. IAM Analyzer provides a clearer picture of these access patterns to assist in removing excessive privileges and working towards the lowest privilege. It can report temporary access sessions and events as well.
Amazon Macie
Data Protection, Amazon Macie helps secure Amazon S3 buckets. It uses machine learning and pattern matching to detect sensitive data within S3 buckets. This alerts you to issues such as lack of encryption or publicly accessible data. This would be particularly beneficial for anyone responsible for compliance.
Amazon GuardDuty
Intelligent Threat Detection, Amazon GuardDuty analyzes stored log data which collected from different AWS accounts and workloads by monitoring Route53 Resolver DNS logs, VPC Flow Logs, event logs, container logs, and other data. Data is analyzed to detect abnormal behavior and present it in a central location using machine learning. Security & SecOps teams would use this service.
AWS Config
Detection and Monitoring, AWS Config will continually evaluate your cloud configurations and detect out-of-policy changes. This is extremely useful when making configuration changes to resources and ensuring that there are no possibilities for data breaches. For example, you can use a drift detection policy to detect manual changes. The target audience is Security Analysts and Cloud Security teams.
AWS Secrets Manager
Sensitive Data Protection, Secrets Manager helps you better protect sensitive information or secrets that allow access to services and databases in your environment. If you need to access a secret, you can create an API call to get the information from the Secrets Manager API. This tool would be beneficial to Development Teams or admins.
AWS Inspector
Detection and Monitoring, AWS Inspector is an assessment service for applications deployed on EC2 instances and container images. Security assessments include CIS benchmarks, potential risks or vulnerabilities (CVEs), or general security best practices, such as disabling root logins for SSH. This would be beneficial for DevSecOps teams or Security Analysts.
AWS Web Application Firewall (WAF)
Infrastructure Security, AWS WAF helps protect web applications from exposure to the internet and therefore from exploitation against OWASP Top Ten Risks. It will detect and mitigate attacks, such as SQL injections. It has managed rules, but your team can customize your own settings. Also, it is already integrated for managed rules to third-party technology partners like F5 and Cisco. This would be beneficial for Cloud, Network, or Security Admins.
AWS CloudTrail
Detection and Monitoring, CloudTrail monitors all behavior in your environment. This includes all actions, requests, responses, and identity operations, and all API calls as events. This will help you review and detect inappropriate or suspicious behavior. For example, you can get notified when the root account is logged in. There is an additional AWS CloudTrail Insights you can add to get alerted when abnormal activity is detected.
Build Upon AWS Security Tools with CloudMetrik
Amazon Web Services has put out comprehensive services and tools to help your teams secure your cloud. That being stated, AWS is a cloud provider, not a security provider. At this point, it is widely accepted that the best way to extend your cloud security beyond the limitations of native tools is to rely on 3rd party security tools.
CloudMetrik exists to serve this purpose and offers a wide variety of solutions, all hosted in one integrated product. Also, we at CloudMetrik have a vulnerability scanner and audit system with over 300 tests, developed by a team of security experts with comprehensive experience. From network systems to business logic, CloudMetrik’s Tool checks all avenues of your system and also provides a comprehensive report for an in-depth understanding of your security standards.